- Automated API vulnerability scanning
- Runtime protection and behavior analysis
- OWASP Top 10 for APIs compliance
- Continuous API security testing for DevSecOps
- External and internal network assessments
- Application and infrastructure penetration testing
- Cloud security assessments (AWS, Azure, GCP)
- Enterprise Key Management Systems (KMS)
- Hardware Security Modules (HSMs)
- Data-at-rest and data-in-transit encryption
- PKI and digital certificate lifecycle management
License Pricing(Annual Subscription)
CYBER RANGES delivers World-Class Cybersecurity Training and Capability Development Exercises using Next-Generation Technology and Services for the Design, Delivery and Management of Simulation-Based, Deep-Dive Experiences in Cybersecurity.
Key Industry Facts on Cybersecurity:DATOS INSIGHTS
Cyber ranges improve first responder effectiveness: cyber range training improves memory retention by 75%, compared to 5% through traditional learning methods.
European Systemic Risk Board
The European Systemic Risk Board (ESRB) estimates the global cost of cyber attacks for the financial sector to be worth $45bn to $654bn.
ISACA
Cybersecurity professionals consider hands-on experience (97%), credentials (88%), and completion of hands-on training courses (83%) as key factors in qualifying candidates.
Team collaboration in a simple way
AI-driven chatbot in the past allowing you to focus more on your business or simply.
Projects and task management
AI-driven chatbot in the past allowing you to focus more on your business or simply.
Centralize your workflows
AI-driven chatbot in the past allowing you to focus more on your business or simply.
CYBER RANGES ON PREMISE Barebone Platform – 424
20 Users Pack
₹1,13,00,000
- ✔ Apache ActiveMQ 5.14.0 Remote Code Execution
- ✔ Apache Solr 7.1 XML Entity Injection Vulnerability
- ✔ Nginx 0.5.6 to 1.13.2 7.1 integer overflow Vulnerability
- ✔ GhostScript Sandbox Bypass (Command Execution)
- ✔ Apache Solr 8.2.0 Remote Code Execution Vulnerability
- ✔ sudo <=1.8.28 Security bypass vulnerability
- ✔ Webmin <=1.920 Webmin Command Injection Vulnerability
- ✔ Girolamo
- ✔ Gelix
- ✔ IFI
- ✔ Xanthos
- ✔ Alphius
50 Users Pack
₹27,120,000
- ✔ Apache ActiveMQ 5.14.0 Remote Code Execution
- ✔ Apache Solr 7.1 XML Entity Injection Vulnerability
- ✔ Nginx 0.5.6 to 1.13.2 7.1 integer overflow Vulnerability
- ✔ GhostScript Sandbox Bypass (Command Execution)
- ✔ Apache Solr 8.2.0 Remote Code Execution Vulnerability
- ✔ sudo <=1.8.28 Security bypass vulnerability
- ✔ Webmin <=1.920 Webmin Command Injection Vulnerability
- ✔ Girolamo
- ✔ Gelix
- ✔ IFI
- ✔ Xanthos
- ✔ Alphius
100 Users Pack
₹5,19,80,000
- ✔ Apache ActiveMQ 5.14.0 Remote Code Execution
- ✔ Apache Solr 7.1 XML Entity Injection Vulnerability
- ✔ Nginx 0.5.6 to 1.13.2 7.1 integer overflow Vulnerability
- ✔ GhostScript Sandbox Bypass (Command Execution)
- ✔ Apache Solr 8.2.0 Remote Code Execution Vulnerability
- ✔ sudo <=1.8.28 Security bypass vulnerability
- ✔ Webmin <=1.920 Webmin Command Injection Vulnerability
- ✔ Girolamo
- ✔ Gelix
- ✔ IFI
- ✔ Xanthos
- ✔ Alphius
200 Users Pack
₹8,08,00,000
- ✔ Apache ActiveMQ 5.14.0 Remote Code Execution
- ✔ Apache Solr 7.1 XML Entity Injection Vulnerability
- ✔ Nginx 0.5.6 to 1.13.2 7.1 integer overflow Vulnerability
- ✔ GhostScript Sandbox Bypass (Command Execution)
- ✔ Apache Solr 8.2.0 Remote Code Execution Vulnerability
- ✔ sudo <=1.8.28 Security bypass vulnerability
- ✔ Webmin <=1.920 Webmin Command Injection Vulnerability
- ✔ Girolamo
- ✔ Gelix
- ✔ IFI
- ✔ Xanthos
- ✔ Alphius
OpenText™ Static Application Security Testing (Fortify) (SAST) identifies and remediates security vulnerabilities in source code with precision. Extensive language coverage and seamless CI/CD integration streamline security across the SDLC. Advanced static code analysis and AI-driven insights prioritize risks and enable developers to resolve vulnerabilities efficiently, reducing overall security risk.
Key feature:
Developer-friendly language coverages
Supports ABAP/BSP, ActionScript, Apex, ASP.NET, C# (.NET), C/C++, Classic, ASP (with VBScript), COBOL, ColdFusion CFML, Go, HTML, Java (including Android), JavaScript /AJAX, JSP, Kotlin, and more.
Flexible deployment options
Includes options such as the SaaS-based OpenText™ Core Application Security Testing platform, private hosted, which combines SaaS and on-premises features, and off-cloud, which offers full control over the application security testing solution.
Real-time code security analysis and results
Provides structural and configuration analyzers that are purpose built for speed and efficiency. Security Assistant only returns high-confidence findings with immediate results in the IDE.
Automation with applied machine learning
Provides automated audit results in minutes, minimizing auditor workload and prioritizing issues with accurate and consistent audit results.
ScanCentral
Enables lightweight packaging on the build server and provides a scalable, centralized scanning infrastructure.
Continuous improvement insights
Leverages data analytics to suggest improvements and optimize workflows.
License Pricing(Annual Subscription)
Onward Security, a DEKRA company, provides IoT cybersecurity compliance solutions. It has been selected as a Hot Company in the Cybersecurity Internet of Things, Global InfoSec Awards. In addition to possessing Asia's most complete cybersecurity assessment lab, it develops security assessment automation tools. It has been dedicated to helping customers in IoT/IIoT device manufacturing, automotive, medical, and other industries to quickly obtain security certification and effectively manage risks and vulnerabilities of software to ensure cyber and product security.
Onward Security Pricing
Orchestra Group products solve the most pressing security concerns for businesses, non-profits and governments. Harmony Purple automates a proven, proactive framework for continuous threat exposure management. Harmony IoT secures the wireless airspace from external and internal threats.
Harmony Purple
Security experts and the analyst community agree – traditional security management programs are failing to protect organizations from cyber threats. This is especially true for small and medium enterprises (SMEs). SMEs are attacked more frequently than large enterprises yet must defend themselves with fewer resources.
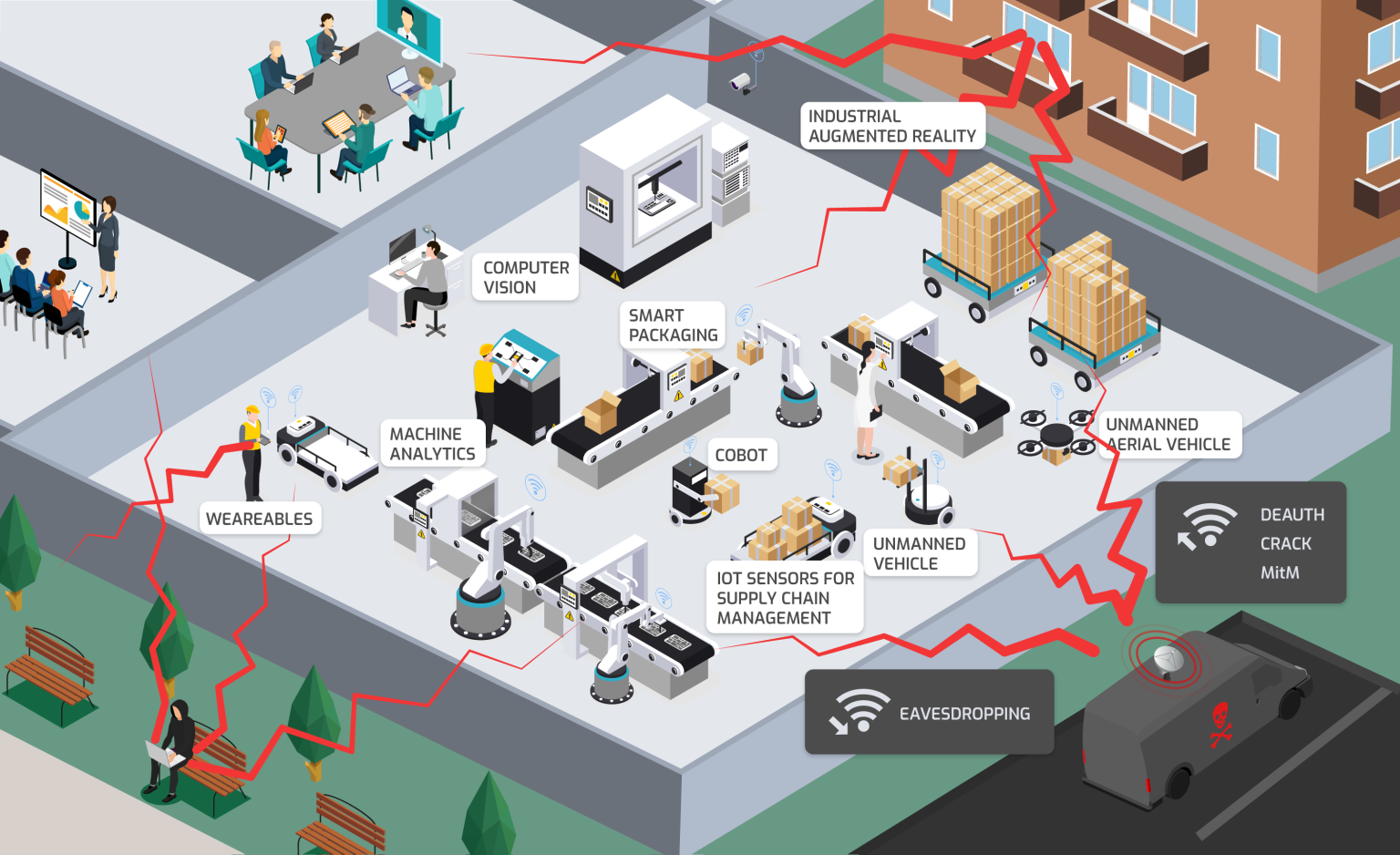
Harmony IoT
In today’s smart-connected world, Harmony IoT delivers an enterprise-grade defense for your airspace that protects you from IoT and wireless-borne attacks.
Harmon IOT Pricing
Harmony Purple Pricing
Software composition analysis solution for safe operations with open source, license compatibility check, sensitive information identification and code quality assessment.
Open Source code inventory
Analyzing code composition, automatically finding package manager configuration files, identifying direct and transitive dependencies from open source software, generating the Software Bill of Materials.
Supply chain protection
Protecting against malicious components, including compromised packages, and offering policies to prevent attacks on the software supply chain. Integrating with Nexus Repository Manager and JFrog Artifactory Pro.
Vulnerabilities in open source
Protecting against malicious components, including compromised packages, and offering policies to prevent attacks on the software supply chain. Integrating with Nexus Repository Manager and JFrog Artifactory Pro.
License compatibility
Determining licenses of detected open source components. Checking their compatibility with each other. Monitoring compliance with the organization's licensing policies.
License Pricing(Annual Subscription)
Quickly find and fix the vulnerabilities that put your applications and APIs at risk of attack. Enjoy more peace of mind – without investing more of your limited time. Thousands of businesses automate application security with Acunetix.
Flexible Packages, Transparent Pricing
No FQDN restrictions. Unlimited coverage. Pay for security, not arbitrary limits.
Essentials
The foundation for a strong AppSec program—begin with certainty.
- ✔ Invicti DAST
- ✔ Internal App Scanning (Agents)
- ✔ Integrations — Ticketing
- ✔ Integrations — CI/CD
- ✔ Predictive Risk Scoring
- ✔ Runtime SCA
- ✔ AST Connectors — SAST only
- ✔ Standard RBAC
- ✔ Standard Support
Recommended Add-Ons:
- ✔ Mend SAST
- ✔ API Security
- ✔ Professional Service Hours
- ✔ Premium Support
- ✔ U.S.-Based Support
Professional
- ✔ Invicti DAST
- ✔ Internal App Scanning (Agents)
- ✔ Integrations — Ticketing
- ✔ Integrations — CI/CD
- ✔ Predictive Risk Scoring
- ✔ Runtime SCA
- ✔ Advanced AST Connectors
- ✔ Standard RBAC
- ✔ Standard Support
- ✔ SSO
Recommended Add-Ons:
- ✔ Mend SAST, SCA, and Container Security
- ✔ API Security
- ✔ IAST
- ✔ Professional Service Hours
- ✔ Premium Support + Guided Success
- ✔ U.S.-Based Support
Ultimate
Comprehensive AppSec for enterprises—maximum security and control.
- ✔ Invicti DAST
- ✔ Internal App Scanning (Agents)
- ✔ Integrations — Ticketing
- ✔ Integrations — CI/CD
- ✔ Predictive Risk Scoring
- ✔ Runtime SCA
- ✔ Advanced AST Connectors
- ✔ Customizable RBAC
- ✔ Premium Support + Guided Success
- ✔ SSO
- ✔ API Security
- ✔ IAST
- ✔ Audit Log
Recommended Add-Ons:
- ✔ Mend SAST, SCA, and Container Security
- ✔ Dedicated Instance
- ✔ Advanced Guided Success
- ✔ Professional Service Hours
- ✔ U.S.-Based Support